-
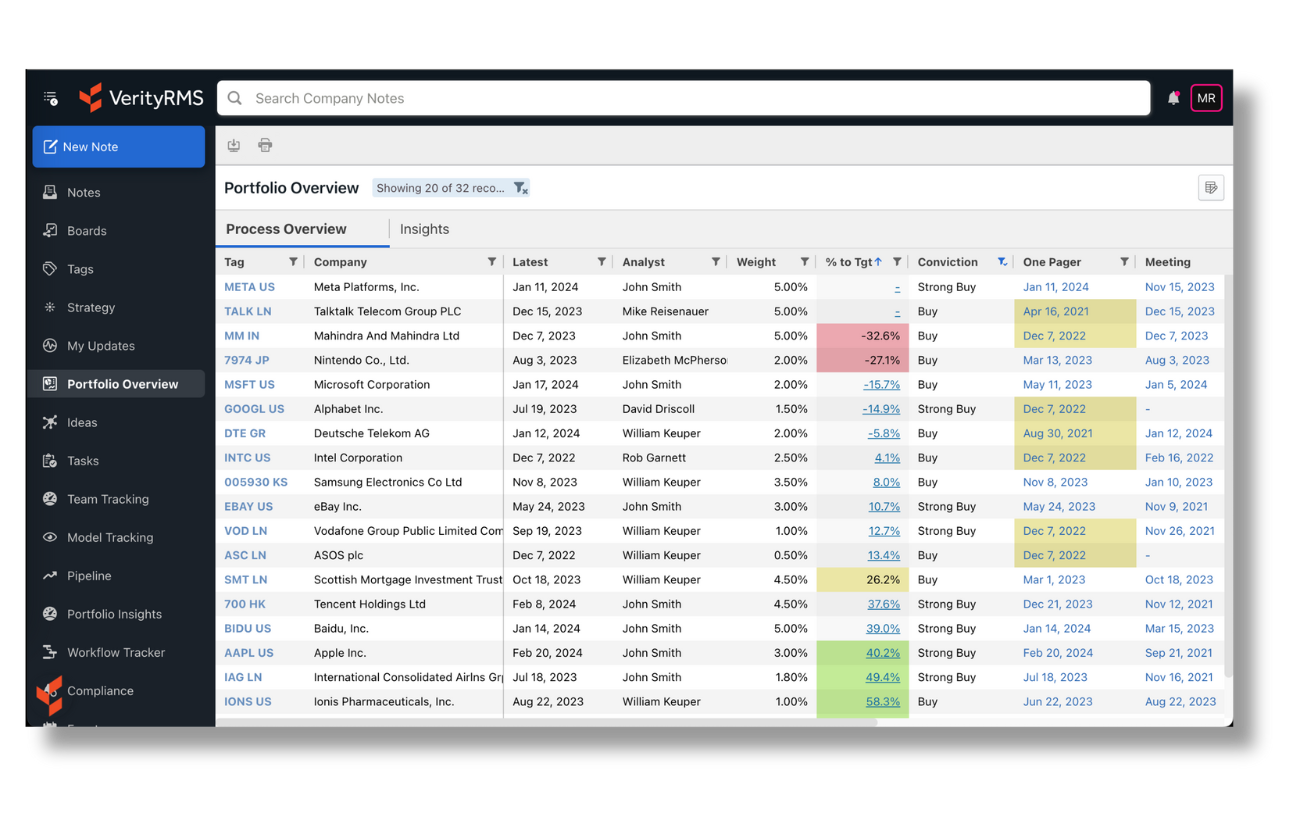
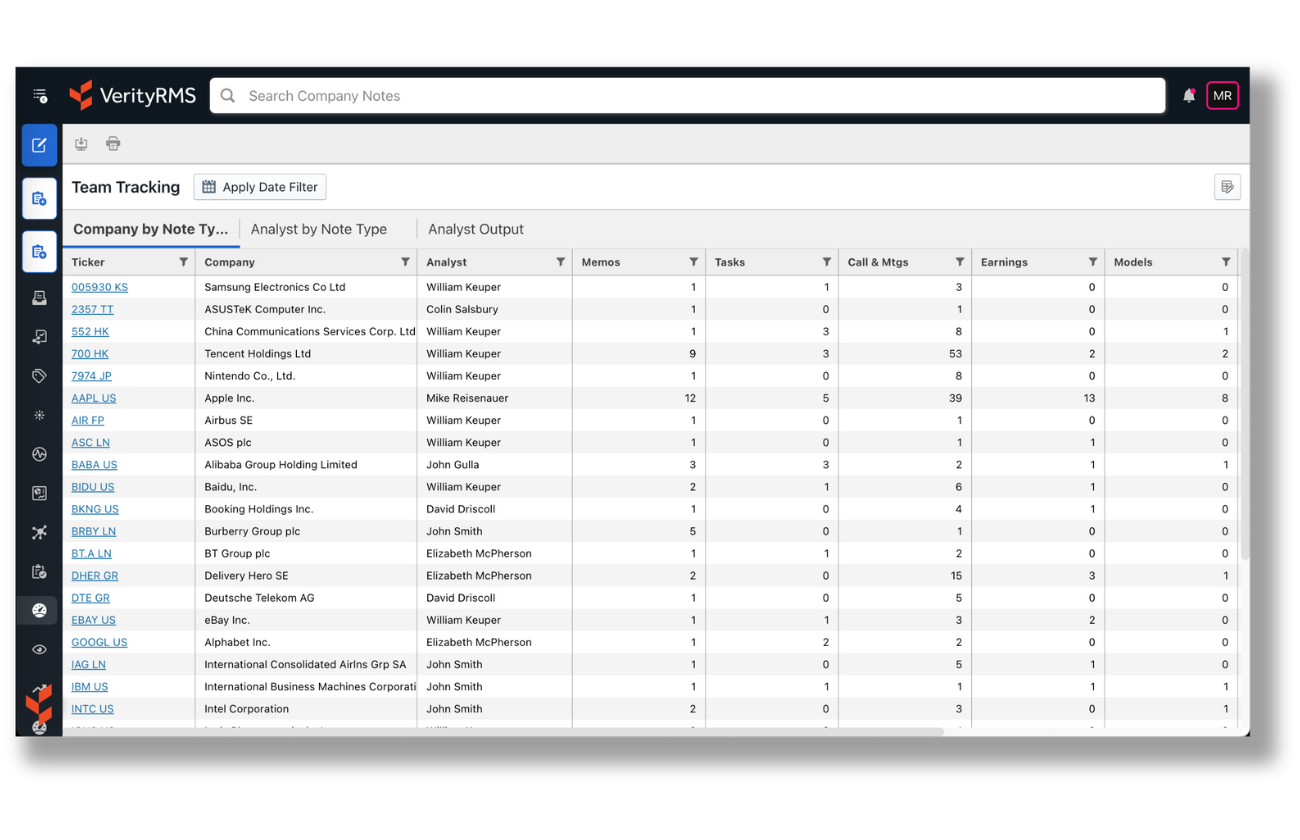
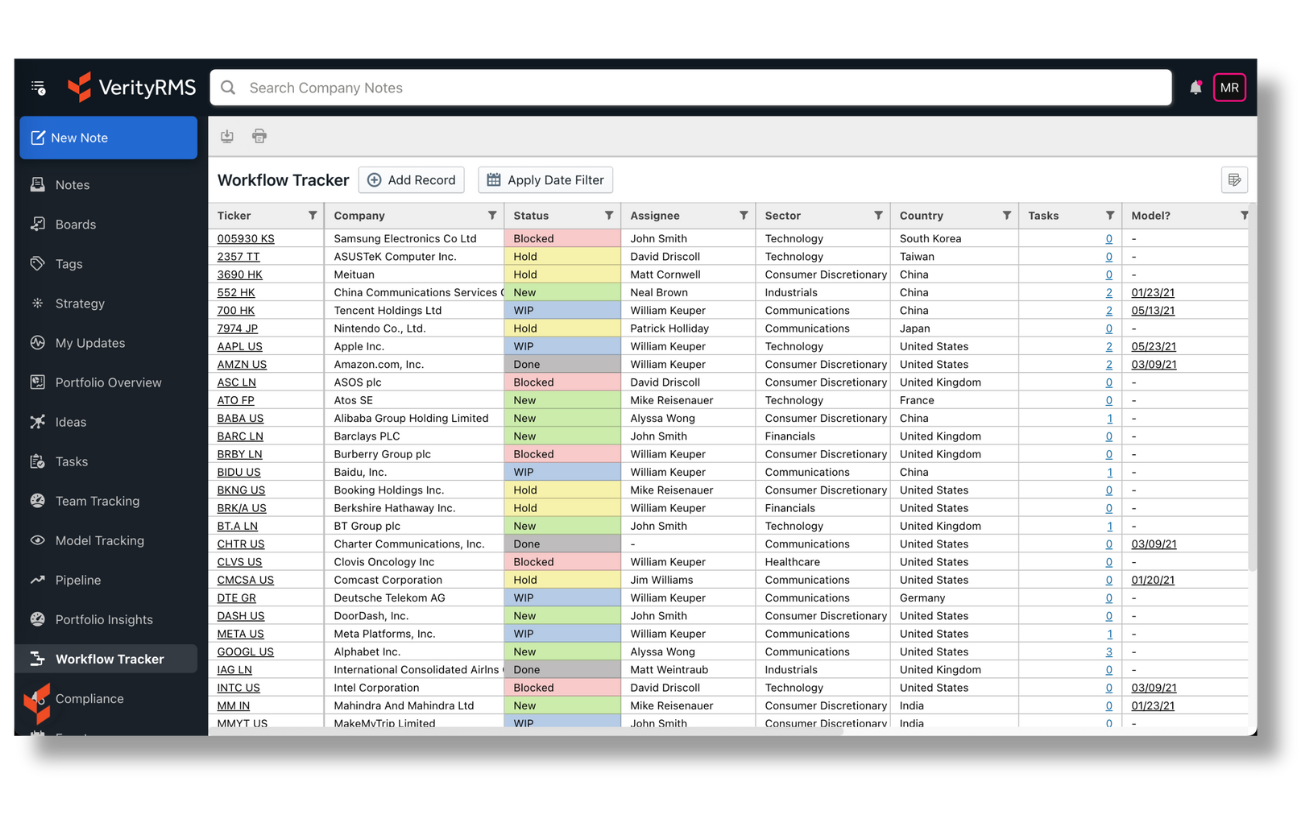
Get real-time alerts & clear visibility into the insights that drive decisions.
-
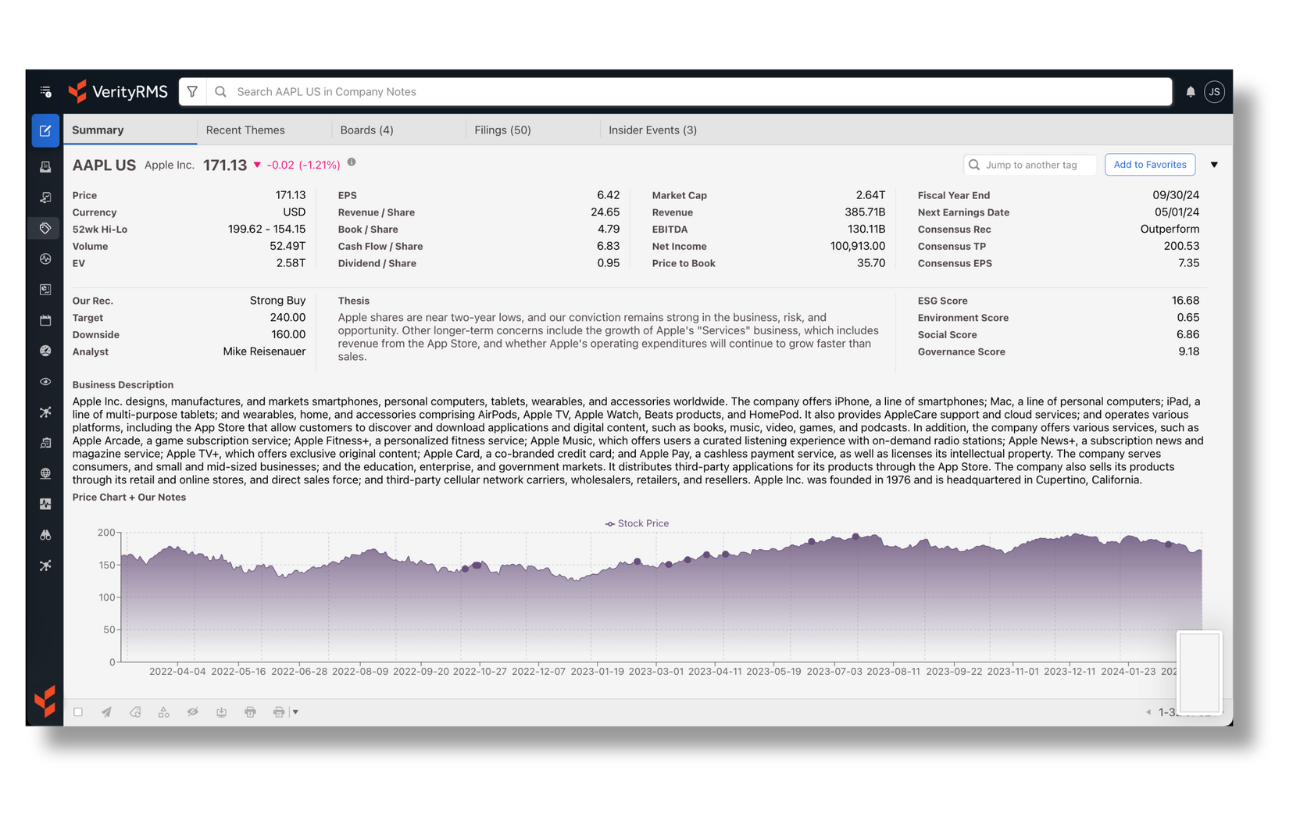
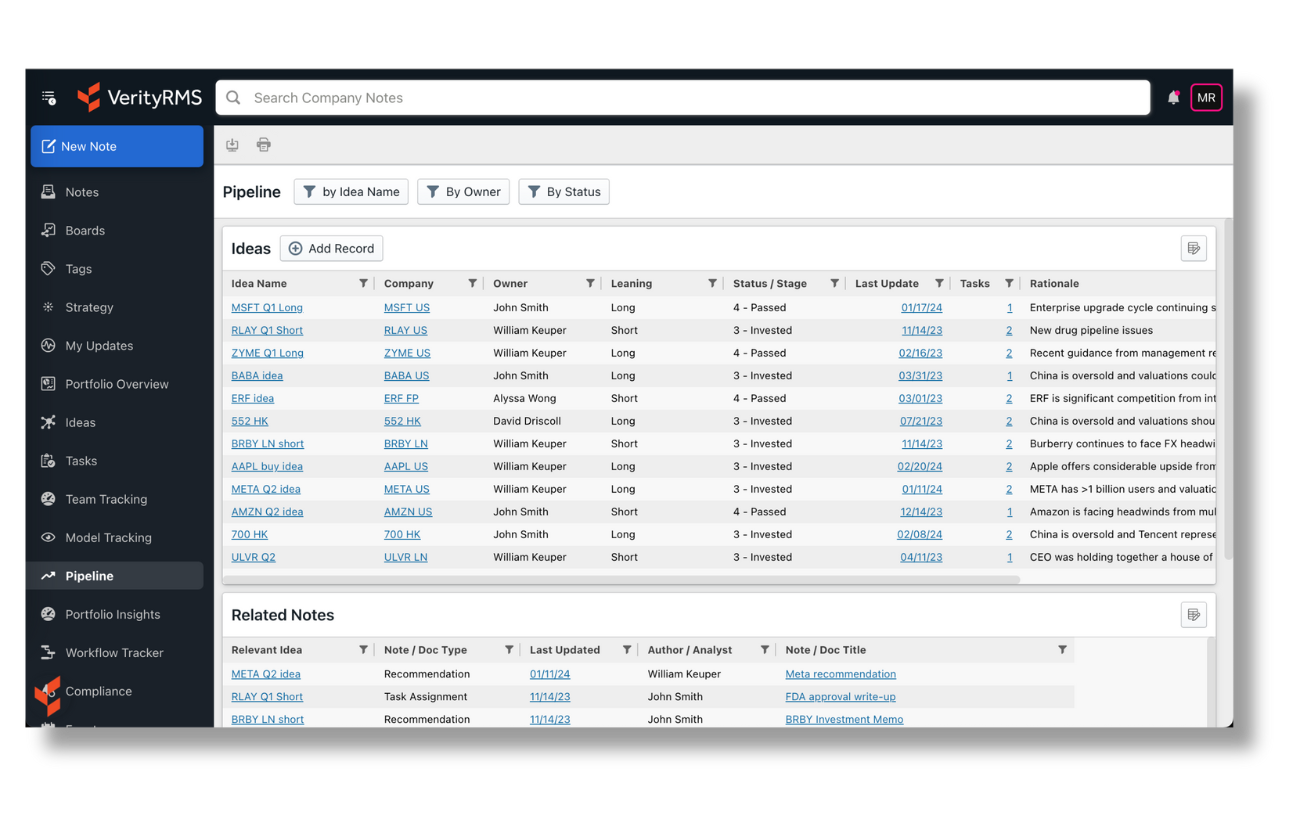
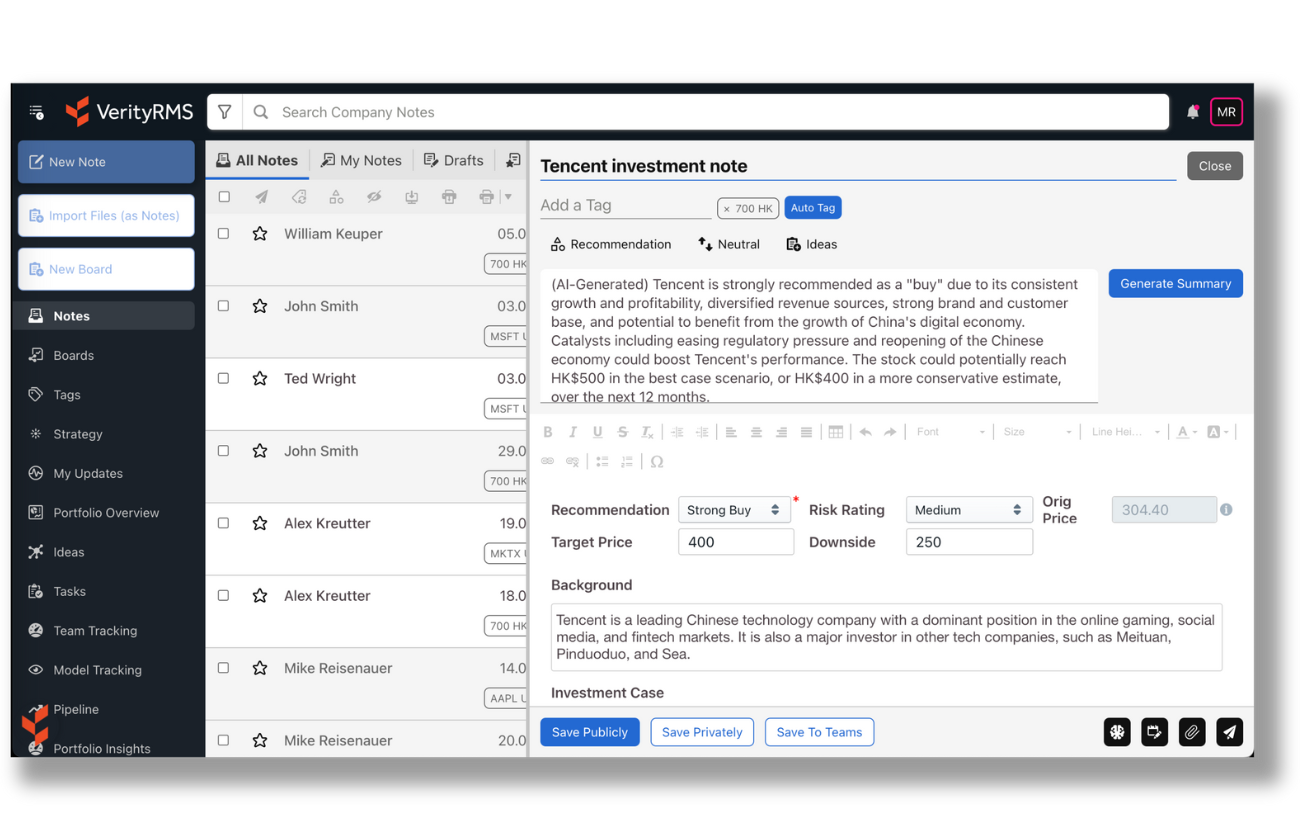
Aggregate data from multiple sources for the context you need.

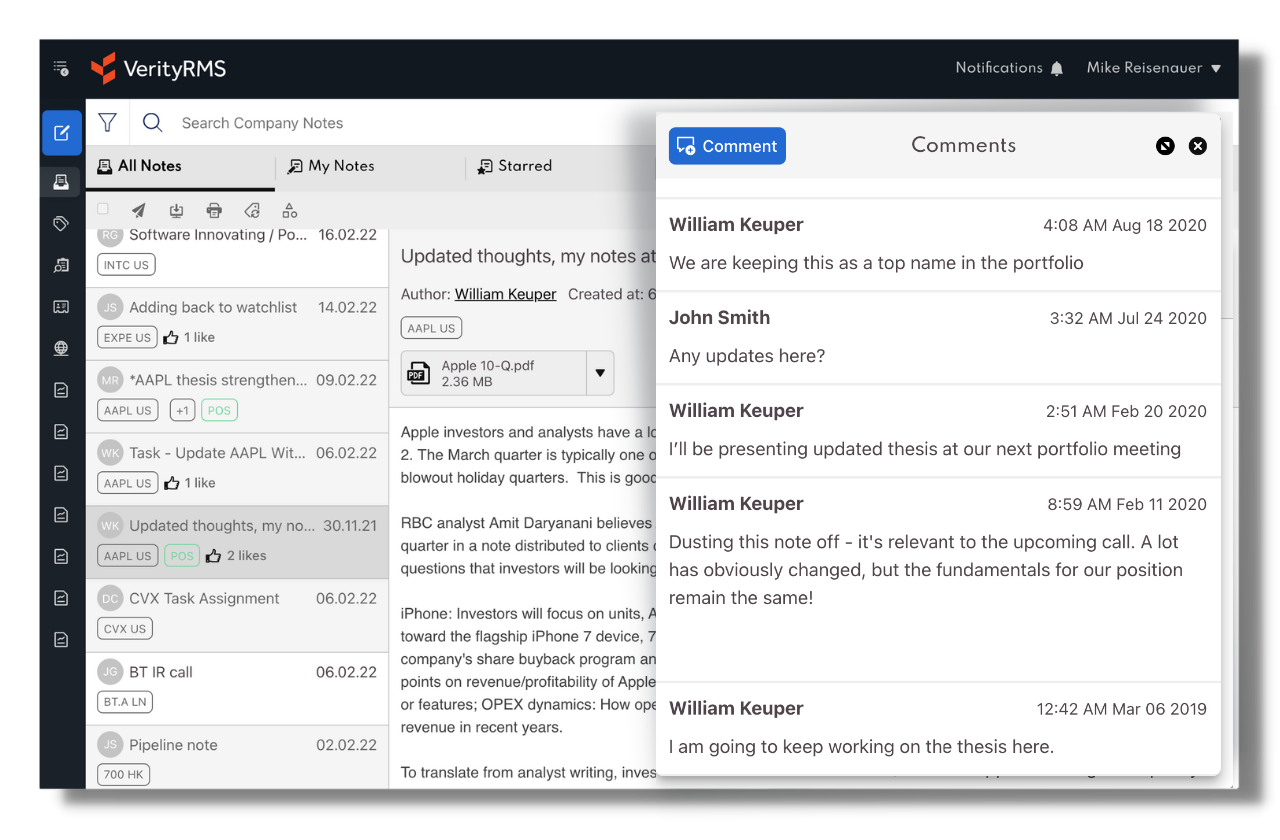
There's no alpha in busywork. Make success automatic with one integrated workspace that improves efficiency, collaboration, & decision-making at scale.
-
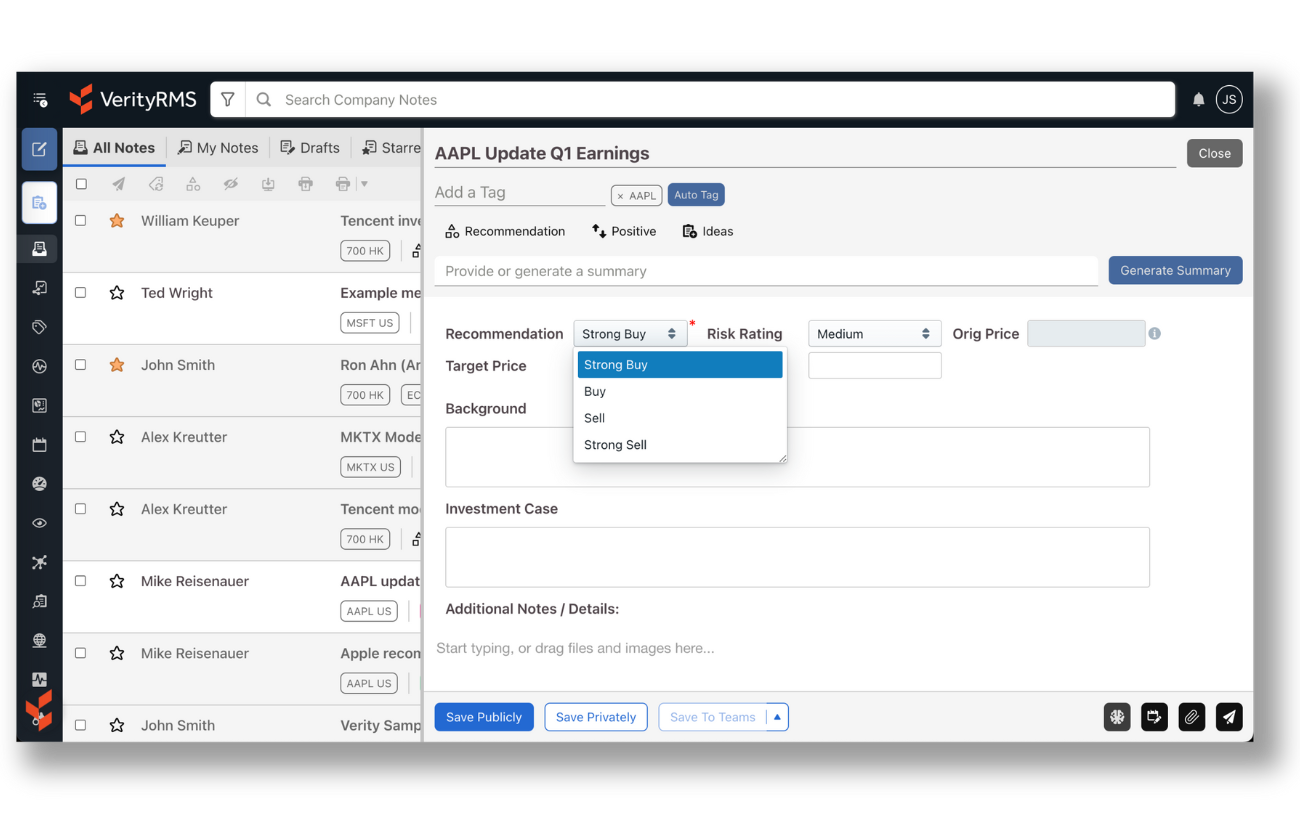
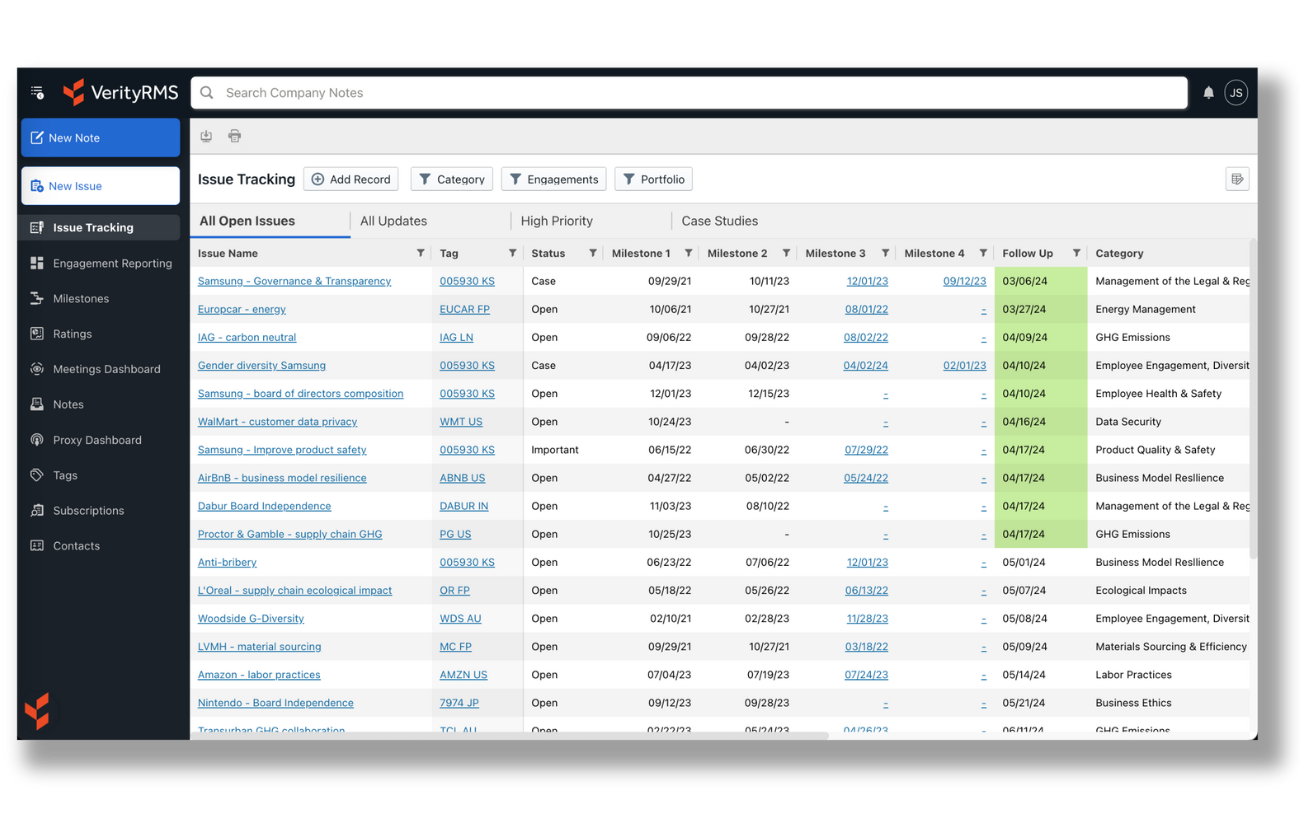
Automate time-consuming manual processes.
-
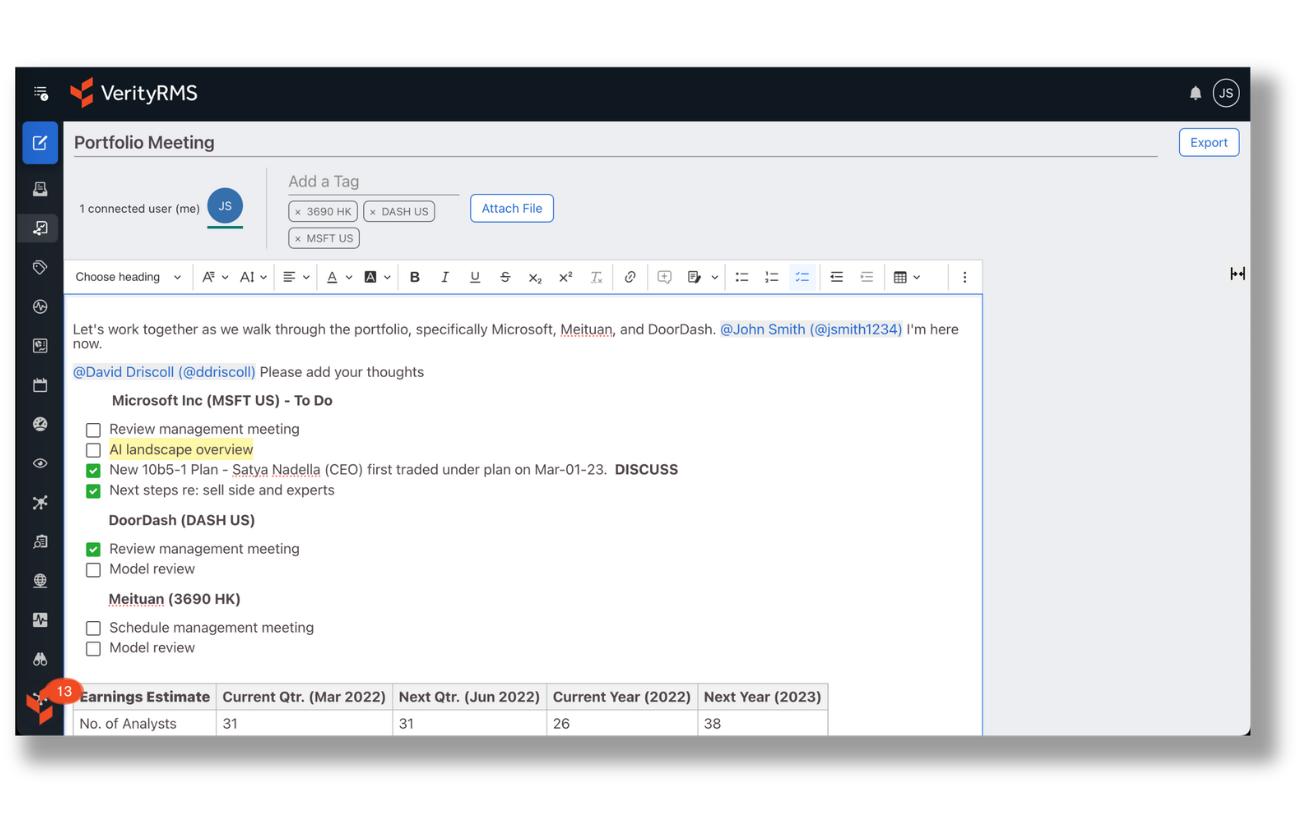
Use purpose-built productivity tools. Boosted by AI.
-
Connect your talent to knowledge, tools, & data they need.
-
Improve transparency for fast, frictionless reporting.
"VerityRMS is a game-changer. The AI innovations are speeding our workflows.”
Director of Research, The London Company


Experience the Power of VerityRMS Research Management System
See how Verity accelerates winning investment decisions for the world's leading asset managers.
Get My Demo